Publications: Optical security
Optical visual encryption using focused beams and convolutional neural networks
Kavan Ahmadi, Artur Carnicer
Optics and Lasers in Engineering 161C, 107321 (2023)
The target of this paper is to implement an optically-based visual encryption system able to work with a large set of optical codes. The optical setup comprises a holographic system designed to generate spirally-polarized highly focused fields and an imaging module able to perform polarimetric analysis. In a previous stage, the optical system is numerically simulated in order to produce synthetic polarimetric distributions that are used to train a convolutional neural network. Interestingly, the way the network is trained depends on the selected state of polarization. Then, secret codes are split in two XOR-connected ones that are optically processed. The corresponding experimental polarimetric distribution is obtained and transmitted to the corresponding recipients, that can recover the code by interrogating the neural network. Finally, combining the two pieces of information, the encrypted message can be decoded.
https://doi.org/10.1016/j.optlaseng.2022.107321
Polarimetric identification of 3D-printed nano particle encoded optical codes
Kavan Ahmadi, Pedro Latorre Carmona, Bahram Javidi, Artur Carnicer
IEEE Photonics Journal 12(3), 1-10 (2019)
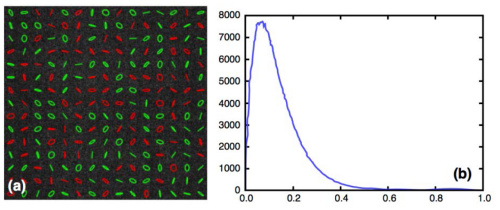
Document signature is a powerful technique used to determine whether a message is tampered or valid. Recently, this concept was extended to optical codes: we demonstrated that the combined use of optical techniques and machine learning algorithms might be able to distinguish among different classes of samples. In the present work, we produce nano particle encoded optical codes with predetermined designs synthesized with a 3D printer. We used conventional polylactic acid filament filled with metallic powder to include the effect of nano-encoding for unique polarimetric signatures. We investigated an interesting real-world scenario, that is, we demonstrate how a single class of codes is distinguished among a group of samples to be rejected. This is a difficult unbalanced problem since the number of polarimetric signatures that characterize the true class is small compared to the complete dataset. Each sample is characterized by analyzing the polarization state of the emerging light. Using the one class-support vector machine algorithm we found high accuracy figures in the recognition of the true class codes. To the best of our knowledge, this is the first report on implementing optical codes with nano particle encoded materials using 3D printing technology.
https://doi.org/10.1109/JPHOT.2020.2987484
Optical security and authentication using nanoscale and thin-film structures
Artur Carnicer, Bahram Javidi
Advances in Optics and Photonics 9(2), 218-256 (2017)
Authentication of encoded information is a popular current trend in optical security. Recent research has proposed the production of secure unclonable ID tags and devices with the use of nanoscale encoding and thin-film deposition fabrication techniques, which are nearly impossible to counterfeit but can be verified using optics and photonics instruments. Present procedures in optical encryption provide secure access to the information, and these techniques are improving daily. Nevertheless, a rightful recipient with access to the decryption key may not be able to validate the authenticity of the message. In other words, there is no simple way to check whether the information has been counterfeited. Metallic nanoparticles may be used in the fabrication process because they provide distinctive polarimetric signatures that can be used for validation. The data is encoded in the optical domain, which can be verified using physical properties with speckle analysis or ellipsometry. Signals obtained from fake and genuine samples are complex and can be difficult to distinguish. For this reason, machine-learning classification algorithms are required in order to determine the authenticity of the encoded data and verify the security of unclonable nanoparticle encoded or thin-film-based ID tags. In this paper, we review recent research on optical validation of messages, ID tags, and codes using nanostructures, thin films, and 3D optical codes. We analyze several case scenarios where optically encoded devices have to be authenticated. Validation requires the combined use of a variety of multi-disciplinary approaches in optical and statistical techniques, and for this reason, the first five sections of this paper are organized as a tutorial.
https://doi.org/10.1364/AOP.9.000218
Optical encryption in the axial domain using beams with arbitrary polarization
Artur Carnicer, Ignasi Juvells, Bahram Javidi, Rosario Martínez-Herrero
Optics and Lasers in Engineering 89, 145-149 (2017)
Recently, a cryptosystem based on the analysis of light in the focal area of a high numerical aperture system has been proposed. A key element in the design of this device is the selection of the polarization of the input beam. In this paper we analyze how polarization influences the performance of the encoded message. In order to avoid attacks and enhance security, the system is assumed to work in photon-counting illumination conditions.
https://doi.org/10.1016/j.optlaseng.2016.06.027
Authentication of gold nanoparticle encoded pharmaceutical tablets using polarimetric signatures
Artur Carnicer, Oriol Arteaga, Josep M. Suñé-Negre, Bahram Javidi
Optics Letters 41, 4507-4510 (2016)
The counterfeiting of pharmaceutical products represents concerns for both industry and the safety of the general public. Falsification produces losses to companies and poses health risks for patients. In order to detect fake pharmaceutical tablets, we propose producing film-coated tablets with gold nanoparticle encoding. These coated tablets contain unique polarimetric signatures. We present experiments to show that ellipsometric optical techniques, in combination with machine learning algorithms, can be used to distinguish genuine and fake samples. To the best of our knowledge, this is the first report using gold nanoparticles encoded with optical polarimetric classifiers to prevent the counterfeiting of pharmaceutical products.
https://doi.org/10.1364/OL.41.004507
Roadmap on optical security
Bahram Javidi, Artur Carnicer, Masahiro Yamaguchi, Takanori Nomura, Elisabet Pérez-Cabré, María S Millán, Naveen K Nishchal, Roberto Torroba, John Fredy Barrera, Wenqi He, Xiang Peng, Adrian Stern, Yair Rivenson, A Alfalou, Cristian Brosseau, Changliang Guo, John T Sheridan, Guohai Situ, Makoto Naruse, Tsutomu Matsumoto, Ignasi Juvells, Enrique Tajahuerce, Jesús Lancis, Wen Chen, Xudong Chen, Pepijn WH Pinkse, Allard P Mosk, Adam Markman
Journal of Optics 18(8) 083001 (2016)
Information security and authentication are important challenges facing society. Recent attacks by hackers on the databases of large commercial and financial companies have demonstrated that more research and development of advanced approaches are necessary to deny unauthorized access to critical data. Free space optical technology has been investigated by many researchers in information security, encryption, and authentication. The main motivation for using optics and photonics for information security is that optical waveforms possess many complex degrees of freedom such as amplitude, phase, polarization, large bandwidth, nonlinear transformations, quantum properties of photons, and multiplexing that can be combined in many ways to make information encryption more secure and more difficult to attack. This roadmap article presents an overview of the potential, recent advances, and challenges of optical security and encryption using free space optics. The roadmap on optical security is comprised of six categories that together include 16 short sections written by authors who have made relevant contributions in this field. The first category of this roadmap describes novel encryption approaches, including secure optical sensing which summarizes double random phase encryption applications and flaws [Yamaguchi], the digital holographic encryption in free space optical technique which describes encryption using multidimensional digital holography [Nomura], simultaneous encryption of multiple signals [Pérez-Cabré], asymmetric methods based on information truncation [Nishchal], and dynamic encryption of video sequences [Torroba]. Asymmetric and one-way cryptosystems are analyzed by Peng. The second category is on compression for encryption. In their respective contributions, Alfalou and Stern propose similar goals involving compressed data and compressive sensing encryption. The very important area of cryptanalysis is the topic of the third category with two sections: Sheridan reviews phase retrieval algorithms to perform different attacks, whereas Situ discusses nonlinear optical encryption techniques and the development of a rigorous optical information security theory. The fourth category with two contributions reports how encryption could be implemented at the nano- or micro-scale. Naruse discusses the use of nanostructures in security applications and Carnicer proposes encoding information in a tightly focused beam. In the fifth category, encryption based on ghost imaging using single-pixel detectors is also considered. In particular, the authors [Chen, Tajahuerce] emphasize the need for more specialized hardware and image processing algorithms. Finally, in the sixth category, Mosk and Javidi analyze in their corresponding papers how quantum imaging can benefit optical encryption systems. Sources that use few photons make encryption systems much more difficult to attack, providing a secure method for authentication.
https://doi.org/10.1088/2040-8978/18/8/083001
Security authentication with a three-dimensional optical phase code using random forest classifier
Adam Markman, Artur Carnicer, Bahram Javidi
Journal of the Optical Society of America A 33(6), 1160-1165 (2016)
An object with a unique three-dimensional (3D) optical phase mask attached is analyzed for security and authentication. These 3D optical phase masks are more difficult to duplicate or to have a mathematical formulation compared with 2D masks and thus have improved security capabilities. A quick response code was modulated using a random 3D optical phase mask generating a 3D optical phase code (OPC). Due to the scattering of light through the 3D OPC, a unique speckle pattern based on the materials and structure in the 3D optical phase mask is generated and recorded on a CCD device. Feature extraction is performed by calculating the mean, variance, skewness, kurtosis, and entropy for each recorded speckle pattern. The random forest classifier is used for authentication. Optical experiments demonstrate the feasibility of the authentication scheme.
https://doi.org/10.1364/JOSAA.33.001160
Optical encryption in the longitudinal domain of focused fields
Artur Carnicer, Ignasi Juvells, Bahram Javidi, Rosario Martínez-Herrero
Optics Express 24(7), 6793-6801 (2016)
We develop a method for encoding information in the longitudinal component of a focused field. Focused beams display a non-zero contribution of the electric field in the direction of propagation. However, the associated irradiance is very weak and difficult to isolate from the transverse part of the beam. For these reasons, the longitudinal component of a focused field could be a good choice for encoding and securing information. Using the Richards and Wolf formalism we show how to encrypt information in the longitudinal domain of the focal area. In addition, we use quantum imaging techniques to enhance the security and to prevent unauthorized access to the information. To the best of our knowledge, this is the first report on using the longitudinal component of the focused fields in optical security.
https://doi.org/10.1364/OE.24.006793
Optical security verification by synthesizing thin films with unique polarimetric signatures
Artur Carnicer, Oriol Arteaga, Esther Pascual, Adolf Canillas, Santiago Vallmitjana, Bahram Javidi, Enric Bertran
Optics Letters 40(22), 5399-5402 (2015)
This Letter reports the production and optical polarimetric verification of codes based on thin-film technology for security applications. Because thin-film structures display distinctive polarization signatures, this data is used to authenticate the message encoded. Samples are analyzed using an imaging ellipsometer able to measure the 16 components of the Mueller matrix. As a result, the behavior of the thin film under polarized light becomes completely characterized. This information is utilized to distinguish among true and false codes by means of correlation. Without the imaging optics the components of the Mueller matrix become noise-like distributions and, consequently, the message encoded is no longer available. Then, a set of Stokes vectors are generated numerically for any polarization state of the illuminating beam and thus, machine learning techniques can be used to perform classification. We show that successful authentication is possible using the k-nearest neighbors algorithm in thin-films codes that have been anisotropically phase-encoded with pseudorandom phase code.
https://doi.org/10.1364/OL.40.005399
Optical encryption using photon-counting polarimetric imaging
David Maluenda, Artur Carnicer, Rosario Martínez-Herrero, Ignasi Juvells, Bahram Javidi
Optics Express 23(2) 655-666 (2015)
We present a polarimetric-based optical encoder for image encryption and verification. A system for generating random polarized vector keys based on a Mach-Zehnder configuration combined with translucent liquid crystal displays in each path of the interferometer is developed. Polarization information of the encrypted signal is retrieved by taking advantage of the information provided by the Stokes parameters. Moreover, photon-counting model is used in the encryption process which provides data sparseness and nonlinear transformation to enhance security. An authorized user with access to the polarization keys and the optical design variables can retrieve and validate the photon-counting plain-text. Optical experimental results demonstrate the feasibility of the encryption method.
https://doi.org/10.1364/OE.23.000655
Security authentication using phase-encoded nanoparticle structures and polarized light
Artur Carnicer, Amir Hassanfiroozi, Pedro Latorre-Carmona, Yi-Pai Huang, Bahram Javidi
Optics Letters 40(2), 135-138 (2015)
Phase-encoded nanostructures such as quick response (QR) codes made of metallic nanoparticles are suggested to be used in security and authentication applications. We present a polarimetric optical method able to authenticate random phase-encoded QR codes. The system is illuminated using polarized light, and the QR code is encoded using a phase-only random mask. Using classification algorithms, it is possible to validate the QR code from the examination of the polarimetric signature of the speckle pattern. We used Kolmogorov–Smirnov statistical test and Support Vector Machine algorithms to authenticate the phase-encoded QR codes using polarimetric signatures.
https://doi.org/10.1364/OL.40.000135
Vulnerability to chosen-cyphertext attacks of optical encryption schemes based on double random phase keys
Artur Carnicer, Mario Montes-Usategui, Sergio Arcos, Ignacio Juvells
Optics Letters 30(13), 1644-1646 (2005)
We show how optical encryption methods based on double random phase keys are vulnerable to an organized attack of the chosen-ciphertext type. The decryption key can be easily obtained by an opponent who has repeated access to either the encryption or decryption machines. However, we have also devised a solution that prevents the attack. Our results cast doubts on the present security of these techniques.
https://doi.org/10.1364/OL.30.001644
Research funded by Ministerio de Ciencia e Innovación, Spain MCIN/AEI / 10.13039/501100011033
- Grant PID2022-136796OB-I00
- Grant PID2019-104268GB-C22
